Fast and secure Mobile Identity verification
Our leading cloud communications platform, best-in-class omnichannel security solutions, and global scale help telcos transform CX and secure the mobile ecosystem for their enterprise, small business, and consumer customers.











[Mobile Identity] security and user experience done right
SILENT MOBILE VERIFICATION
Instantly verify users with their mobile number
- Secure verification which eliminates friction on service sign-up and login without interruption
- Streamlines online transactions, shortening the buying cycle
- Elevates your NET promoter score and prevents churn
- Simple integration with existing tech stack

SIM SWAP CHECK
Identify and prevent SIM swap fraud
- Prevents fraud before it impacts the customer, using real-time insights
- Reduces the number of false positive verifications
- Minimizes manual security interventions
- Complies with PSD2 SCA & GDPR regulations

NATIONAL IDENTITY NUMBER MATCH
Prevent unwanted access to services with National ID number match
- Check if the claimed user ID number matches the ID number the user registered with on his local mobile operator
- Improve the security of your onboarding process
- Reduces fake registrations and synthetic identity fraud

Boost customer experience securely
Protect customers during account activation
Easily identify the customer’s mobile number while they are activating their online account without interrupting the customer experience.
Protect customer accounts during everyday use
Use secure and simple user authentication without compromising the customer experience.
Improve the onboarding customer experience
Easily validate user information during the registration or login process, while keeping the customer flow uninterrupted.
Increase number of app users
Identify new users when activating the mobile app easily, without interrupting the customer experience.
Infobip API
Use any programmable language to easily integrate various communication channels and modules into your business workflows.
Why should you use Infobip’s all-in-one customer engagement solution?
Optimize interactions
Leverage customer data to understand your customers and send personalized messages that create meaningful interactions across the customer journey
Build loyalty and trust
From onboarding to purchase – harness the power of automation, behavioral and event triggers, and send time optimization to deliver the right messages at the right time across to boost loyalty.
Increase revenue
Boost your upsell, cross-sell and lead generation efforts with a combination of personalized campaigns and a conversational chatbot to keep customers engaged.
Enhance customer engagement
Deliver efficient and personalized customer experiences to gain a competitive advantage in today’s digital environment.
Discover more about Mobile Identity
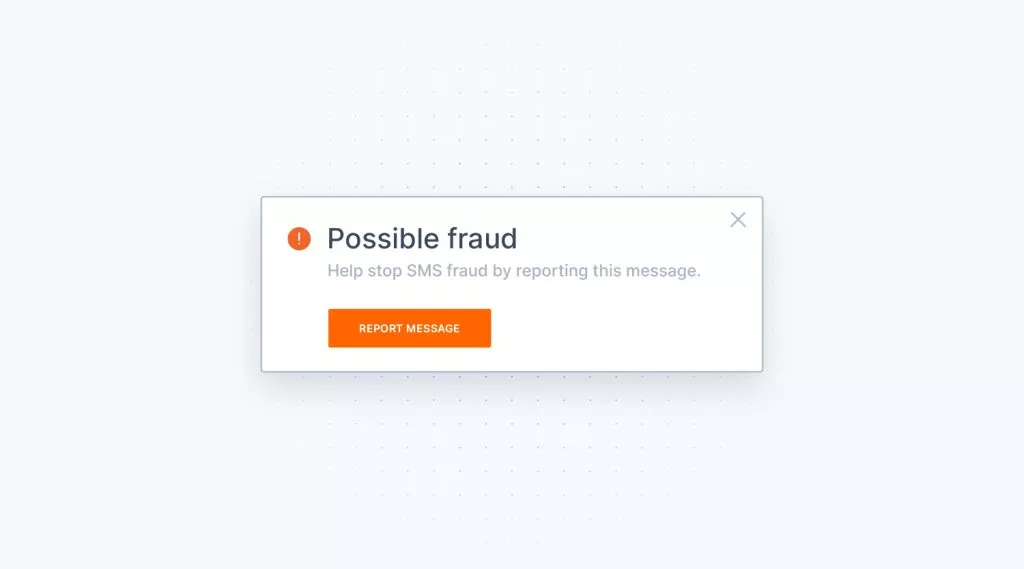
A complete guide to SMS fraud detection and prevention
Learn about the latest SMS fraud tactics criminals are using, how they work, and how they can be prevented.

SMS Flubot: How Telcos Can Protect End-Users
Discover how to get ahead of malicious flubot attacks and protect your customers and your business from potential threats.

Why Infobip is the Ideal Telco Partner
The right communication technology partner can help telcos add customer value and deliver business efficiencies resulting in new revenue streams.




