The rising threat of SIM swap fraud and how to protect your business
Learn about the dangers of SIM swapping fraud, and what can be done to prevent it from causing serious financial loss.

SIM swap fraud has exploded from a telecom concern into a universal threat impacting all industries. Recent cyberattacks on major retailers like M&S and Harrods show that any business handling customer data is now at risk. In just the first half of 2024, SIM swap incidents in the UK surged by over 1,000%, with £5.35 million in financial losses attributed to SIM swap fraud between 2023 and 2024.
The fallout goes beyond financial damage. Communications fraud now threatens brand reputation, disrupts supply chains, and erodes customer trust. As cyber threats evolve, businesses must shift their focus from simply maintaining service to actively safeguarding sensitive data, especially as regulatory scrutiny and potential fines intensify.
No business, regardless of size or sector, can afford to treat communications security as optional. Advanced, layered security and firewall are now essential for protecting customer data, maintaining trust, and safeguarding business operations.
What is SIM swap fraud?
At its core, SIM swap fraud is a form of account takeover fraud and Cybercrime where scammers exploit the process of swapping SIM cards to access a victim’s personal and financial information. They gain unauthorized control over the victim’s phone number, which enables them to take over social media or bank accounts.
In short, here’s how it works:
- Cybercriminals legally or illegally get access to your data (including mobile phone number) and contact mobile network operators (MNOs) pretending to be you.
- They deceive the MNOs into activating a new SIM card with your phone number.
- Once the new SIM card is activated, fraudsters can access every one-time-pin (OTP) and two-factor authentication (2FA) message sent to that number, effectively gaining access to all your accounts that use your phone number for verification.
This lets them receive all calls and SMS messages sent to the original number, including OTPs and 2FA codes used by banks, retailers, and online services for two factor authentication.
Armed with access to these codes, fraudsters can reset passwords, drain bank accounts, make unauthorized purchases, and steal sensitive business data.
Social engineering is at the heart of most SIM swap attacks, with fraudsters exploiting personal data from breaches or phishing, and sometimes even recruiting insiders within telecom operators (BioCatch/Financial Times, May 2023).
Why is SIM swap fraud on the rise?
SIM swap fraud thrives due to our growing dependence on phone numbers for security key accounts, oversharing personal information online, and gaps in telecom security practices.
When personal details are easily accessible through social media or data breaches, scammers can impersonate victims and convince mobile operators to transfer their number to a new SIM card, often bypassing weak verification steps.
This enables attackers to gain control of sensitive accounts protected by two-factor authentication, putting both individuals and businesses at risk.
Several other trends are fueling the dramatic spike in SIM swap fraud:
- Widespread reliance on SMS and OTPs for verifying digital identity means a single compromised phone number can unlock multiple accounts.
- Massive data breaches across industries have put personal information needed to pull off a SIM swap within easy reach of attackers.
- AI and automation make it easier than ever for fraudsters to launch convincing phishing attacks and social engineering campaigns at scale.
The result? SIM swap fraud is now a top risk not just for telecoms but also for retailers, eCommerce providers, banks, fintech, and consumers worldwide. In the U.S., the FBI estimates average losses of $10,000 per victim (IC3 Report). As more businesses move to mobile, this risk will only grow.
Impact of SIM swap on Retail & eCommerce and how to prevent it
Trust and revenue at stake
SIM swap attacks are increasingly targeting retailers and eCommerce platforms. These attacks can result in unauthorized purchases, emptied loyalty accounts, lost revenue, data breach, and customer access.
These incidents don’t just mean financial losses, they can also trigger operational disruptions and long-term reputational damage. When high-profile breaches make headlines, brands risk losing the very trust they’ve built with their customers.
How can businesses protect themselves and their customers?
Effective SIM swap fraud prevention in retail and eCommerce starts with layered security:
- Integrate SIM swap detection from network APIs into fraud prevention workflows. If a SIM swap is detected, require extra identity verification—such as biometric authentication—before allowing sensitive actions like high-value purchases or password changes.
- Combine telco data with behavioral analytics to flag suspicious login attempts, location changes, or account updates.
- Educate customers at critical touchpoints (like checkout and profile updates) about the risks of SIM swap attacks and best practices for digital identity protection.
Impact of SIM swap on telecom operators and how to prevent it?
Telecom operators occupy a unique position as both frequent targets and frontline defenders against SIM swap fraud. If attackers slip past weak verification processes, telcos can face regulatory fines, customer churn, operational costs, and severe reputational harm. The responsibility to detect and prevent SIM swaps is greater than ever.
Best-in-class telecom security now includes:
- AI-driven analytics to monitor for abnormal SIM swap patterns—such as mass porting events or sudden changes in user location.
- Stricter internal controls: Limiting and rotating employee access to SIM management systems, and enforcing multi-factor authentication for staff.
- Active customer confirmation: Requiring direct digital approval from customers before processing any SIM changes, closing a key social engineering loophole.
Impact of SIM swap on banks & financial services and how to prevent it
For banks, fintechs, and financial service providers, SIM swap fraud can swiftly undermine SMS-based two-factor authentication, opening the door to direct financial theft, regulatory breaches, and customer attrition.
The speed and scale of SIM swap-enabled attacks make robust fraud prevention critical in financial services.
Leading financial institutions are adopting a multi-layered approach:
- Adopt out-of-band authentication methods such as secure banking apps, push notifications, or voice biometrics instead of relying solely on SMS OTPs.
- Monitor recent SIM activity: Flag accounts with recently swapped SIMs and require additional verification for high-risk transactions.
- Establish real-time data sharing with telcos via network APIs, so that suspicious activity can be detected and stopped before funds are lost.
How to detect and prevent SIM swap fraud?
To detect SIM swap fraud, businesses can check for changes to a mobile user’s phone number (MSISDN) and International Mobile Subscriber Identity (IMSI) number.
An IMSI number is unique to each SIM card and is used to identify every mobile phone subscriber on a UMTS or GSM network. The IMSI remains unchanged even when a mobile (MSISDN) number is ported to a different SIM card.
Our Mobile identity solution can assist enterprises in mitigating SIM swapping by recent changes in the MSISDN – IMSI combination on the side of the mobile operator.
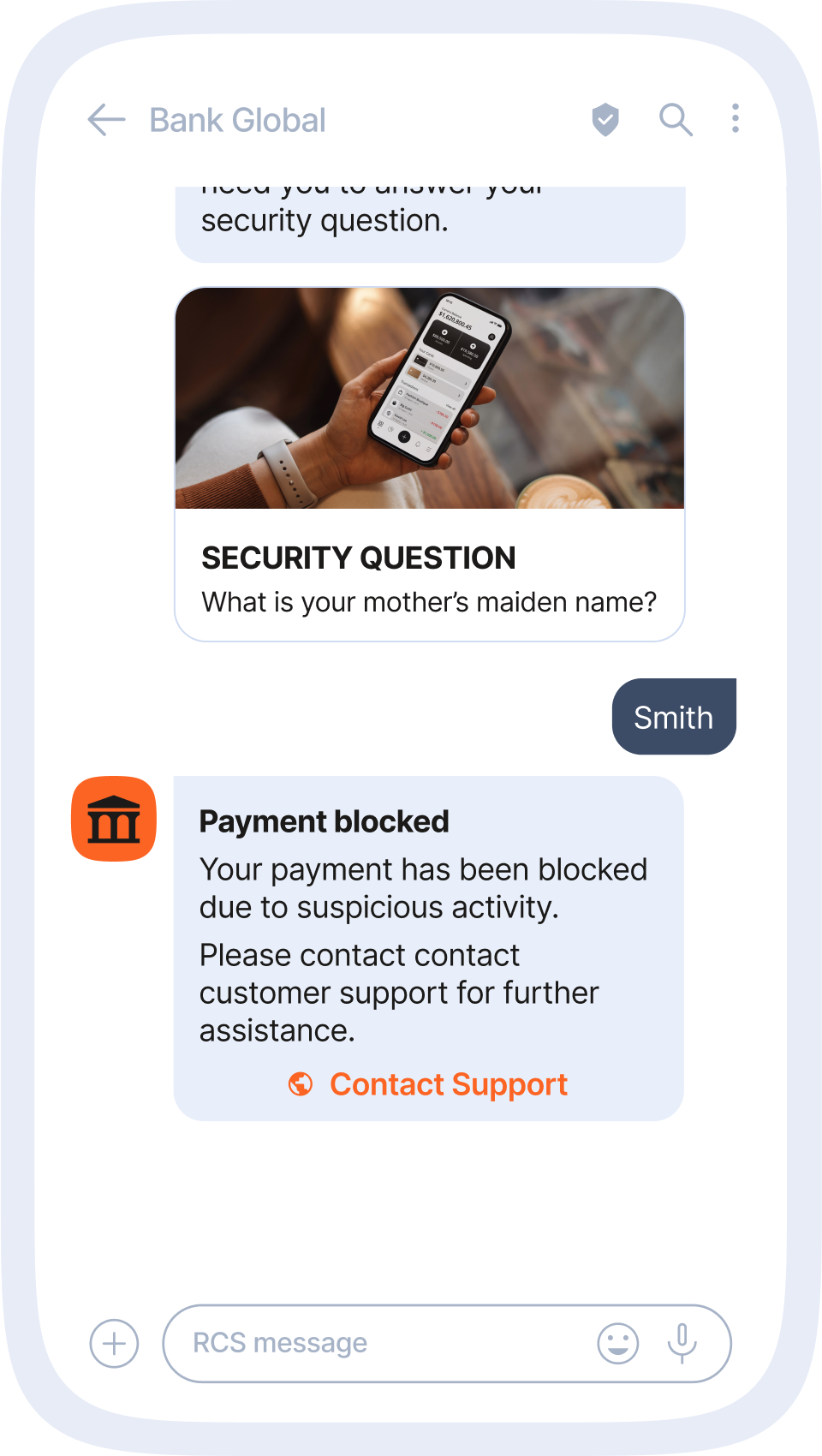
For example, when a bank sends OTP codes for user verification, it may also carry out a SIM swap check. This will ensure the bank isn’t sending a verification code to a fraudster who has acquired a new SIM card with the same mobile number as the account they are attempting to hack.
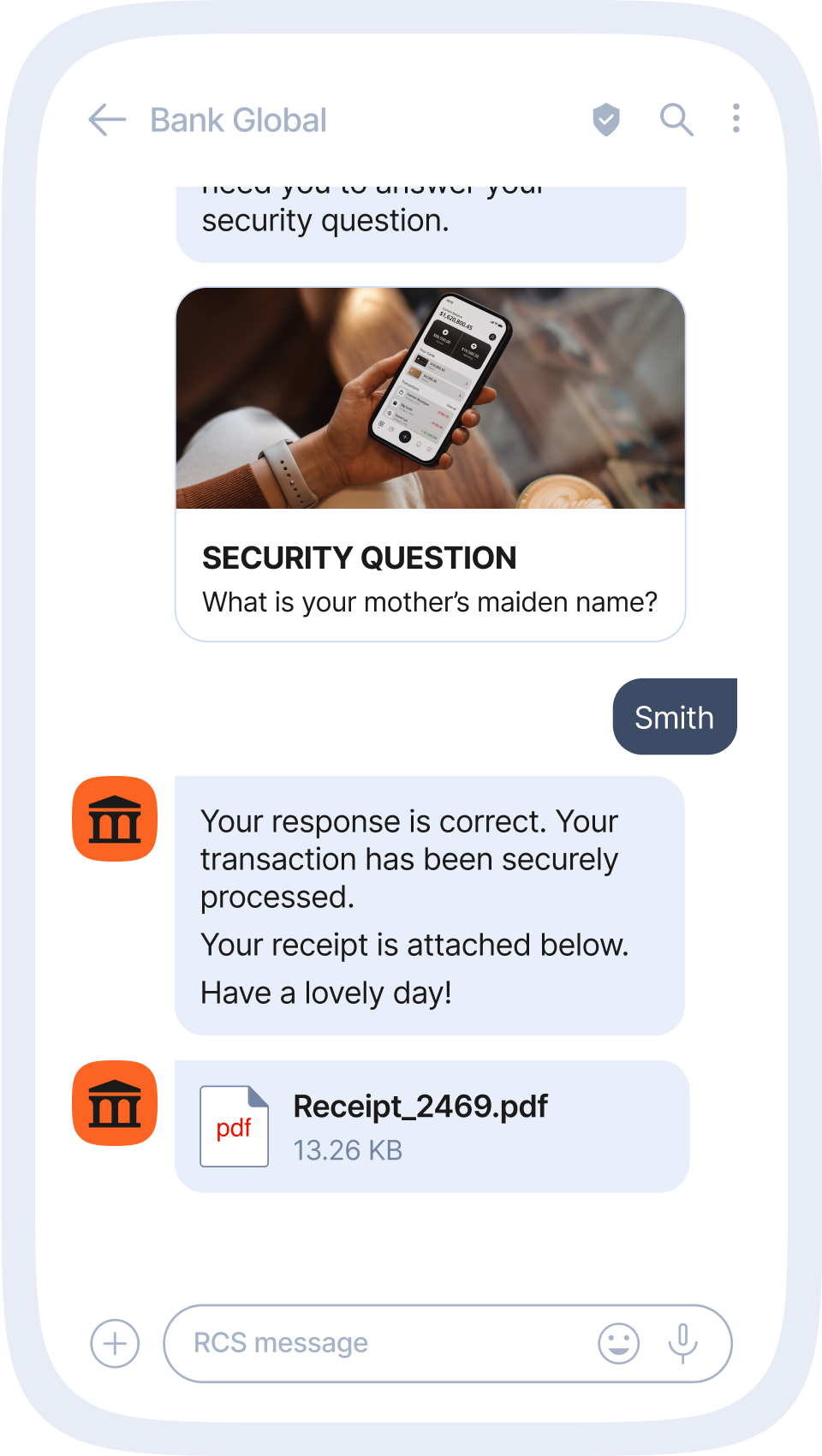
In other words, it can provide information on which phone number is currently assigned to a particular SIM card. Most commonly, business trigger a SIM swap check right before a high-risk action, such as a large transaction or password reset, to ensure the request is coming from the legitimate user. If a SIM swap is detected, businesses can require additional verification before allowing the action to be taken.
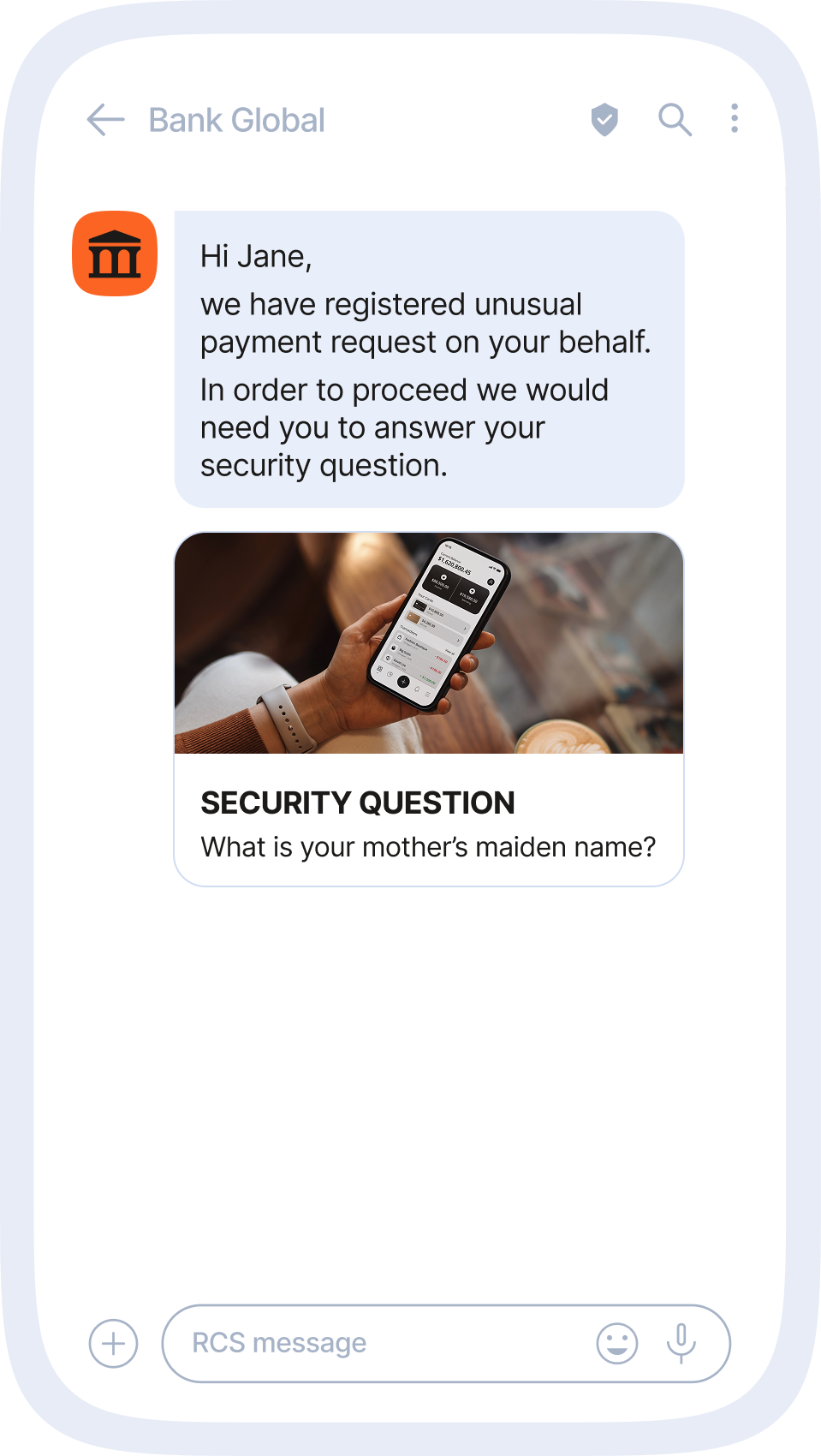
Strengthening fraud prevention with RCS and Network APIs
Combining Rich Communication Services (RCS) with Network APIs gives telcos and enterprises a smarter, more secure way to deliver trusted and high-impact messaging.
APIs for SIM swap detection, Silent Number Verification, Know Your Customer (KYC) checks, and device location enable businesses to build fraud protection and identity assurance directly into the messaging flow, without adding friction for users.
Delivered through RCS with verified sender profiles, these interactions feel seamless to customers while giving businesses more control and security than traditional SMS or OTT apps.
As demand for secure, high-engagement channels grows, Network APIs become a new source of value. By offering them alongside RCS as a managed service, operators can position themselves as trusted technology partners while generating new revenue through API consumption.
Infobip’s role in securing the ecosystem from SIM swap fraud
Working with businesses across industries, we can confidently say that effective SIM swap fraud prevention is never about one tool or one policy. It’s about layering the right technologies, processes, and ongoing education.
As attackers evolve their tactics, businesses must adapt, updating their strategies to protect their customers, their brand, and their bottom line.
Here’s how we help businesses stay protected:
- Real-time network intelligence: Our SIM Swap Detection API instantly alerts you to SIM changes, so you can pause suspicious activity and require extra verification before fraud occurs.
- Modern network firewalls: Anam Protect detects and blocks unauthorized SIM swaps and suspicious port-outs at the network edge.
- Stronger mobile identity verification: Silent verification, device-binding, and biometrics reduce dependence on vulnerable SMS codes.
- RCS fraud prevention: Verified RCS business messaging, complete with brand logos and sender checkmarks, ensures secure and trusted customer communication.
- AI and behavioral analytics: We flag unusual behaviors, such as device swapping or rapid transaction patterns, allowing for fast, targeted intervention.
What sets our approach apart is a commitment to ongoing vigilance, customer education, and close collaboration with industry partners. Fraud tactics never stand still, neither do we.
Every business is a target, but you can take action!
SIM swapping fraud is not just a telecom issue or a banking risk. It is a serious threat that can lead to significant financial loss and reputational damage. However, by taking proactive measures, both individual mobile users and businesses can significantly reduce the risk and consequences.
Ultimately, staying ahead of attackers requires continuous effort, collaboration, and adaptation. Businesses that prioritize security at every level, the right technology, process, and people are best positioned to safeguard their customers, protect their reputation, and thrive in today’s mobile-first world.