Research: How mobile fraud prevention is a team effort
Join us as we look at the latest IDC Infobrief into securing mobile communications in a digital world, and what mobile fraud solutions are available to each stakeholder to help them do their part to preserve the integrity of the mobile eco-system.

Whether you are a business owner, a mobile subscriber, or you work for a network operator, we all have at least one thing in common. Right now, our mobile phones are either in our pockets, next to us on our desks, or perhaps in our hands as we read this.
That means that we are all at risk of falling victim to mobile fraud. The next time your phone pings with an SMS or a message notification, it could be a genuine or it could be yet another attempt by a fraudster to get you to clink on a link, provide personal details, or even ask you to pay a sum of money to get a parcel delivered that you never ordered.
You may think that you are too savvy to become a victim, but fraudsters are continually evolving their tactics, using social engineering tactics to gather information that makes their approaches more believable. Or maybe you will just get unlucky – you may get that SMS asking you to arrange delivery of your parcel right after you ordered that item that you are super excited to receive. It could happen to any of us.
But what can we do about it? How can we solve a problem that is continually changing, like a Rubik’s cube whose tiles continually change color?

In this blog we take a closer look at the findings of IDC’s Infobrief Securing Mobile Communications in a Digital World and show how collaboration between all stakeholders is the only way to address the problem of mobile fraud. We also look at what mobile fraud prevention solutions are available to each type of organization.
$11.6 billion
Global spending on security in the telecom sector in 2022.
33%
The proportion of enterprise business leaders that said improved security measures were required in their organizations.
34%
The proportion of decision makers that said security and compliance was their top consideration when selecting a CPaaS provider.
What do we mean by SMS fraud?
If you are not familiar with the different types of SMS fraud that the report deals with, it is worth reading our detailed guide on SMS fraud which describes each in detail. Here is a short summary:
- Smishing is a type of fraud where criminals contact potential victims by SMS or other type of message to trick them into providing personal information or bank account information or clicking on links that that download malware onto their phones.
- Spoofing: SMS spoofing is a way of changing the sender information on a text so that the recipient sees whatever alphanumeric text is defined, rather than a mobile number. While not actually illegal in many regions, it is a tactic used by fraudsters to mimic messages from legitimate businesses as part of smishing attacks.
- SIM swapping: SIM swap fraud happens when cyber criminals contact MNOs pretending to be a customer and trick them into activating a new SIM card with the customer’s phone number. Once this is done, the scammer has full access to the end-user’s phone and information. Every one-time-pin (OTP) and 2FA message that is sent to that specific number is received by the fraudster.
- SMS pumping: Also known as artificially inflated traffic (AIT) or toll-free fraud, it is a type of SMS fraud that can radically increase your SMS bill when fraudsters artificially inflate your SMS traffic by sending you fake OTP messages.
- SMS grey routes: SMS grey routes represent a type of fraud committed by rogue mobile operators where A2P SMS messages, which should be charged at a premium rate, are passed off as P2P traffic for all or parts of their journey to benefit from reduced rates.
- SMS SPAM: While the impact on mobile subscribers is perhaps not as serious as other types of fraud, SMS spam breaks compliance laws in most countries around the world and leads to an overall degradation of trust in SMS as an effective business communication channel.
What is the current state of mobile fraud prevention?
As more and more consumers become victims of messaging fraud, enterprise businesses are well aware of the potential impact on their business models. The IDC report paints a very clear picture of how companies are taking the threat seriously and ramping up their spending on preventative measures.
Just some of these include:
- 33% of enterprise business leaders said that protection against security threats needs urgent improvement in their organizations
- Spending on security in the telecom sector reached $11.6 billion globally and will grow at a CAGR of 13.3% during the forecast period
- The most important consideration stated by decision makers when selecting a CPaaS provider was security and compliance capabilities at 34% – above customer support at 33%.
How each stakeholder can help solve mobile fraud
The IDC report makes it very clear that any solution to mobile fraud has to be a unified effort including all players in the mobile messaging ecosystem. This includes MNOs, enterprises, regulators, and firewall providers.
We would add to this that a shift in public awareness and increased alertness to potential SMS fraud are also of key importance. If fraudsters are not being successful, then they will stop wasting time for diminishing returns.
But what can each stakeholder actually do? And what anti-fraud solutions are available to each?
Mobile Network Operators (MNOs)
MNOs are in a difficult position as they need to adequately protect their subscribers from fraud by blocking messaging scams and SIM box fraud, but if they go too far and block legitimate traffic then they will be eroding their revenues and negatively impacting their customers who may miss out on key messages like authentication OTPs.
The solution for MNOs is to invest in advanced SMS firewall security that uses AI to accurately detect and filter out fraudulent traffic while allowing the traffic from legitimate businesses to be delivered reliably.
In addition, by being able to identify grey route traffic and filter it through legitimate paid routes then they are able to protect their revenue and provide a better service to their partners and subscribers.
Our SMS firewall solution is one of the most advanced and sophisticated available to MNOs. The benefits are clear for all stakeholders in the messaging ecosystem:
- Subscribers benefit by having fraudulent and SPAM messages blocked.
- MNOs benefit from increased revenues and reduced customer complaints about valid messages being blocked.
- Better monitoring and traffic segmentation enables tighter control of the entire messaging network, benefiting all parties.
Regulators
Regulatory agencies are in a difficult position. They play an important role in protecting the interests and privacy of individuals, but at the same time by enforcing rigid privacy regulations they may prevent MNOs from getting maximum benefit from the capabilities of SMS firewalls, for example content filtering, real-time blocking, and local-source blocking. This would in turn impact individuals by exposing them to more fraud attempts and spam traffic.
The key is to find the right balance between privacy and the effectiveness of network security measures like SMS firewalls. This requires regulatory agencies to work with MNOs and A2P vendors to ensure mobile users are protected from fraud and their privacy is not endangered.
Find out how how telcos can navigate the European regulatory landscape securely with our insightful blog.
Enterprises
For enterprises that rely on OTPs to authenticate transactions there is a critical need to protect themselves from artificially inflated OTP traffic which is when fraudsters use bots to send multiple OTP requests – causing a massive increase in their messaging costs.
The best way of doing this is to partner with a CPaaS provider who can safeguard your OTP traffic using a variety of technology-driven techniques. For example, fraudsters will often use a range of different numbers to mount an attack to remain undetected for as long as possible. Our Signals solution can automatically detect the series of numbers sending OTP requests and block them, or where a single number has sent multiple requests to a range of businesses in a short space of time it can be identified and blocked.
At Next, we are committed to protecting our customers from fraud while continuing to provide the rich, responsive, and reliable communication that they expect from us. To benefit from the latest anti-fraud technology, we partnered with Infobip to empower us to be proactive in keeping both our customers and infrastructure safe from new and emerging threats. Their AI and machine-learning powered solution Infobip Signals, helped block approximately 175,000 artificial messages per month, enabling us to maintain the reliability and security of our SMS messaging by mitigating the risk of fraudulent activity. This means that our customers always receive updates on time, and we can continue to deliver the personalized promotional messaging that they expect.
Raz Razaq,
Domain Manager, Customer Contact Experience Technology, Next
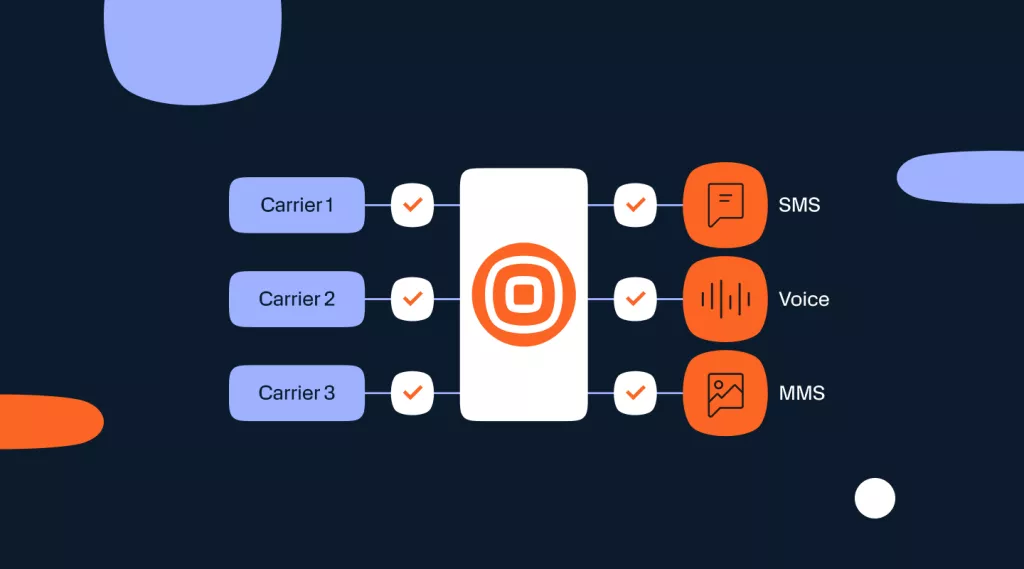
With our evolved CPaaS solution brands can also easily explore the use of different channels for the sending of authentication messages. We can ensure maximum channel flexibility with minimum engineering effect with the largest range of supported channels of any vendor, including:
Technology solution provider checklists
When evaluating technology partners, stakeholders in the messaging ecosystem need to look at a wide variety of factors beyond cost and their ability to meet service levels. With IDC research showing that the most important consideration stated by decision makers when considering a technology partner was security and compliance, here are some pointers for finding a partner that can meet your high expectations.
Firewall providers
Firewall providers need to ensure that their solutions consistently enforce the highest security and privacy standards.
- Continually monitor for new threats and ensure their solutions can protect against them
- Offer content processing based on machine learning to reduce the requirement for human intervention.
- Protect end-users’ privacy by separating out metadata or anonymizing data.
- Provide real-time protection without the delays that give fraudsters a window of opportunity.
CPaaS providers
Not all CPaaS solutions offer the same levels of security and monitoring of the traffic that passes through their infrastructure. We aim to continually evolve our solutions to combat new threats and enable businesses to protect their customers on every channel that they use.
Rather than offering a one-size-fits-all approach to the provision of cloud communication services, with CPaaS X we provide the flexibility to adapt solutions according to the requirements of each customer and use-case.
These include specific features to help combat fraud:
- Automatic detection of fraudulent and bot-generated traffic
- Proactive analysis of overall traffic for early identification of possible issues
- Provide real-time alerts and immediately actionable insights
A2P messaging providers
Some providers will make promises about delivery rates and the volumes of messages that they can handle at a low price, but will often stay quiet on how they can achieve this, perhaps by utilizing grey routes or partnering with network operators with less stringent security protocols.
Here are a few guidelines for choosing a provider that can securely handle your A2P traffic.
- They should partner with established and highly regarded network operators around the world to ensure the highest security standards and best deliverability rates for messages.
- Maintain a global presence and uniform high levels of service with strategically placed data centers across all regions of the world.
- Provide robust, accurate, and easy-to-access reporting capability so that potential fraud can be identified early and negated.
- Provide 24/7 global support so that any security threats can reported and acted upon before they impact your business.