Blog
Explore a wide range of topics, get inspired by the latest trends, and learn how to create conversational experiences that make an impact on your bottom line.

Posted onMarch 4, 2026.
Best conversational AI platforms.
The best conversational AI platforms are not defined by features alone, but by how well they integrate into your strategy, systems, and customer experience.
Tags:- Blog.
- Conversational experience.
- Best Practices.
- Trends and Insights.
Posted onMarch 3, 2026.
Add a WhatsApp button to your website: Easy set up guide for 2026.
Learn how to add a WhatsApp chat button to your website. WordPress, HTML, and website builders supported, easy setup, benefits, features, and best practices.
Tags:- WhatsApp Business.
- Best Practices.

Posted onMarch 3, 2026.
WhatsApp shop: How to create a WhatsApp store and sell in chat.
Learn how to create a WhatsApp Shop and sell directly in chat. Step-by-step guide to WhatsApp store setup, eCommerce integration, catalogs, payments, and website integration.
Tags:- Blog.
- eCommerce.
- WhatsApp Business.
- Best Practices.
Posted onMarch 2, 2026.
The compliance tax: How regulatory fragmentation is eating your roadmap.
Global messaging compliance has become a continuous engineering workload. Learn how regulatory fragmentation is becoming a hidden tax on product roadmaps.
Tags:- Blog.
- Awareness.
- Best Practices.
Posted onMarch 2, 2026.
Best marketing automation platforms in 2026 .
Compare the best marketing automation platforms in 2026. Learn which solutions unify customer data from marketing, sales, and service, orchestrate seamless multi-channel campaigns across email, SMS, WhatsApp and more, and deliver AI-powered personalization at scale.
Tags:- Blog.
- Blog.
- Marketing.
- Trends and Insights.
Posted onFebruary 27, 2026.
Best enterprise AI agent solutions in 2026.
Looking for the best enterprise AI agent solutions? Compare 7 top platforms by channel coverage, compliance, and integration depth.
Tags:- Blog.
- Awareness.

Posted onFebruary 25, 2026.
Best WhatsApp API providers for business in 2026.
Big conversations need the right engine. In this guide, you will discover the top WhatsApp API providers for 2026, what sets them apart, and how to choose a platform that grows with you, not just for you.
Tags:- Conversational experience.
- Customer Service.
- Marketing.
- WhatsApp Business.
- Best Practices.

Posted onFebruary 24, 2026.
99Pay & Infobip: Expanding access to credit through intelligent communication.
How 99Pay is using RCS to scale efficiency, elevate experience, and bring more Brazilians closer to credit.
Tags:- Blog.
- Conversational experience.
- RCS.
- Inspiration.
- Spotlight.

Posted onFebruary 23, 2026.
Digital banking transformation: RBI’s customer engagement strategy.
Find out how RBI's digital transformation balances AI automation with customer engagement using Infobip's omnichannel platform across 10 CEE markets.
Tags:- Blog.
- Financial Services.
- Awareness.
- Spotlight.
Posted onFebruary 23, 2026.
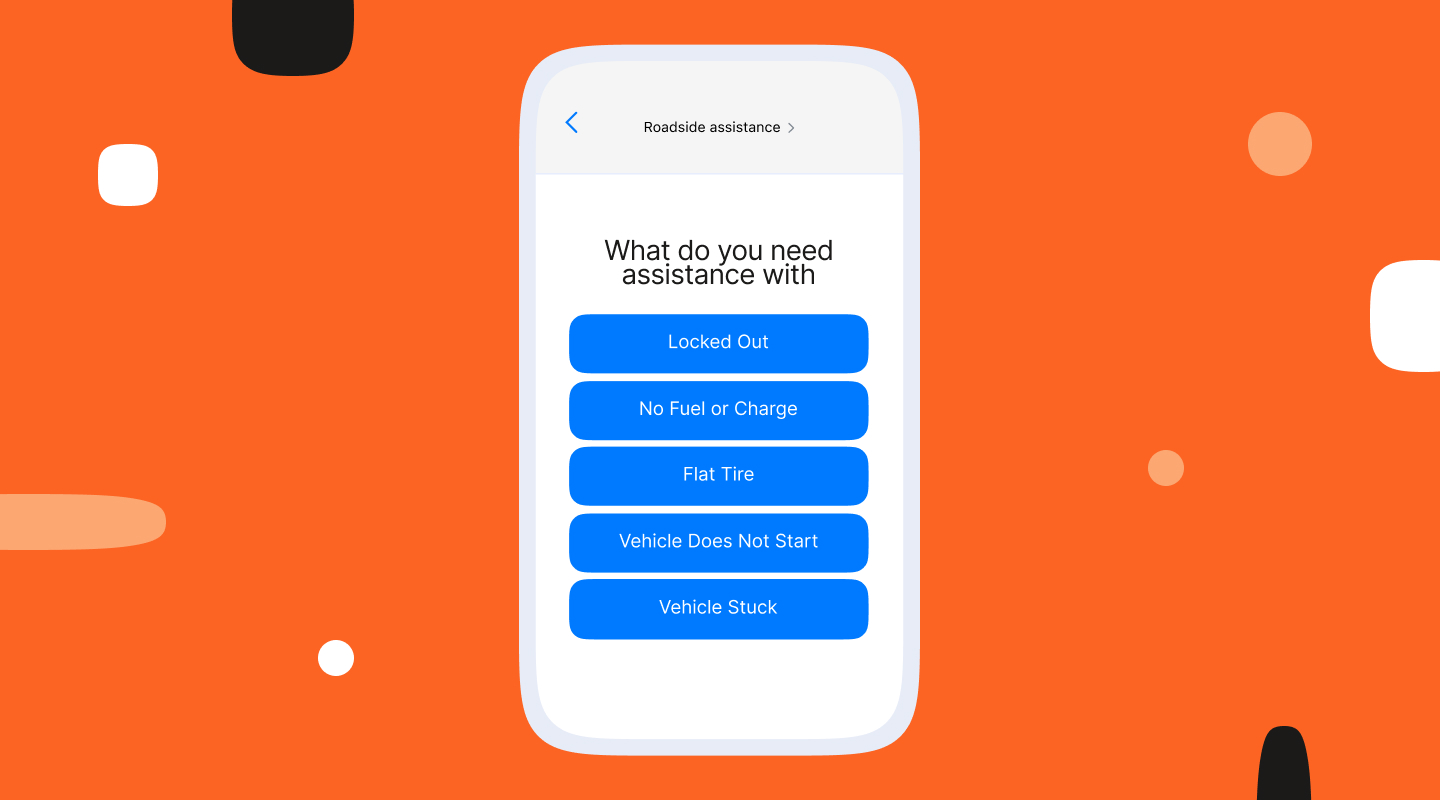
No signal, no problem: Your iPhone can connect you to roadside assistance for help.
Apple's Roadside Assistance via satellite lets iPhone 14 or later connect to orbiting satellites to send messages when no mobile signal is available. Learn how.
Tags:- Blog.
- Awareness.

Posted onFebruary 20, 2026.
Sagent Group: Building customer engagement strategies that start with outcomes.
Customer engagement works best when it starts with outcomes, not products. Here is how Sagent Group and Infobip make it happen.
Tags:- Blog.
- Conversational experience.
- Best Practices.
- Trends and Insights.
- Spotlight.
Posted onFebruary 19, 2026.
WhatsApp marketing automation: Promotional messages, setup, templates.
WhatsApp marketing automation for promotional messages, with setup steps and templates. Comprehensive tools comparison and best practices used in 2026.
Tags:- Blog.
- Marketing.
- WhatsApp Business.
- Awareness.
Posted on{{date_formatted}}.
{{title}}.
{{excerpt}}
Tags:- {{term.name}}.